1) Differentiate between abstract class and Interface in Java?
Abstract class and interface both concepts are used to accomplish abstraction in Java. The primary differences between abstract class and Interface are:
- The abstract keyword is used to create an abstract class in Java, whereas interface keyword is used to create Interface.
- An abstract class can have both abstract and non-abstract methods whereas Interface can only have abstract methods.
- As a general class, abstract class also does not support multiple inheritance, whereas an interface supports multiple inheritance.
- An abstract class can extend other class and implement interfaces but an interface cannot extend class. It can only extend other interfaces.
- An abstract class may or may not have methods with implementations, but Interface cannot have method implementation.
2) What are the static variable and static block?
Static variable: If we use the static keyword with a variable then it is termed as a static variable. Static variables are the part of the class not, the instance. When we declare any static variable, then it creates a copy in memory which is shared between all the objects. Static variables are not thread safe as it is shared between various objects. Static variables are mainly used for memory management.
Syntax:
- static variable_name;
Static Block: A block inside a class with the static keyword is called a static block. A static block is executed at the time of class loading and before the execution of the main method. Static block is primarily used for initialization of the static variable. A class can have multiple static blocks, and they execute in the sequence as they appear in the program.
Syntax:
- static{
- // code to be executed
- }
3) What do you understand by TCP/IP?
TCP/IP stands for Transmission Control Protocol/Internet Protocol. It is a suite of protocols TCP and IP, used for the communication over a network. TCP/IP protocols provide some standard rules for communication between two or more computers over the network. The TCP protocol at the transport layer divides a message or data into packets form and then resembled the packets at the destination part. IP protocol at Network layer is responsible for the moving of these packets to the correct destination.
4) Which is the fastest sorting algorithm?
There is no such specific fastest sorting algorithm because it depends on various factors and all the sorting algorithm gives different performances for different input cases. Although among all the sorting algorithm we can consider Quicksort as a fastest algorithm as it shows time complexity of O(n log n) for the best case and average case and O(n^2) for the worst case.
5) What is tunnelling and tunnelling protocols? Explain their applications?
Tunnelling is also known as port forwarding. These are the communication protocols which allow the secure data movement from one network to another network. Tunnelling enables communication from the private network which sent across the public network, and such process is called as encapsulation.
In tunnelling process, data is converted into the form of packets, which travels through the tunnel. As data packets are moving through the tunnel, they got encrypted by the encapsulation process and when these packets reach the correct destination, then these packets are de-encapsulated and de-encrypted, and the packets again converted to the original data.
Main tunnelling protocols are:
- PPTP: PPTP stands for the point-to-point tunnelling protocol. PPTP is available for Windows, Linux, and Mac. This protocol keeps data secure even in the public network. It works with the virtual private network which can be accessed by an authorized user.
- L2TP: L2TP stands for Layer 2 tunnelling protocol, which supports VPN. It depends on the encryption protocol for the encryption of data which passes through the tunnel.
Application of tunnelling protocols:
- Tunnelling is used in cases where high-level security is required for data transmission over the network.
- It is helpful for encryption and decryption of data.
6) Explain Polymorphism in Java?
Polymorphism in Java is an important feature of Object Oriented Programming (OOP), which defines a single object with different forms. With the help of polymorphism, one action can be done in various ways.
There are mainly two types of polymorphism in Java:
- Run-time polymorphism
- Compile-time polymorphism
Run-time polymorphism: Method overriding is used to achieve Runtime polymorphism. It is also called Dynamic polymorphism or Dynamic method dispatch. In Run-time polymorphism, when we call an override method, it is resolved at run-time, hence it is called as run-time polymorphism.
Compile-time polymorphism: Method Overloading is used to achieve the Compile time polymorphism. It is also called as Static polymorphism and when we call the method, it is resolved at compile time only. That’s why it is called as Compile-time polymorphism.
7) What do you understand by Pointer arithmetic in C?
As we know Pointer is a variable which holds the address of another variable and that variable is a numeric value, so any arithmetic operation performed on a pointer is termed as pointer arithmetic. But we can only perform some limited arithmetic operations on the pointer, which are given below:
- Increment
- Decrement
- Addition
- Subtraction
- Comparison
8) Explain the difference between packet switching and circuit switching?
The Packet switching and circuit switching both are the switching methods which are used to forward the data packets from the sender to receiver destination.
The main differences between the Packet switching and circuit switching are given below:
| Packet Switching | Circuit Switching |
|---|---|
| In packet switching, data is divided into small parts, termed as packets and then these packets are transmitted from source to destination. | In circuit switching a physical path is established between two endpoints for data transmission. |
| Packet switching is connectionless | Circuit Switching is connection oriented. |
| Packet switching can be implemented at the network layer of the OSI model. | Circuit switching can be implemented at the physical layer of the OSI model. |
| It is mainly designed for data and voice communication. | It is basically designed for voice communication. |
| Congestion occurs at the time of data transfer phase. | Congestion occurs at the time of connection establishment. |
9) What do you understand by CDMA?
CDMA is the acronym for Code-division multiple access, is a standard for the wireless digital cellular network. CDMA is a type of multiplexer, where various transmitters can transmit information simultaneously over a single communication channel. CDMA uses spread-spectrum technology and special coding scheme for data transmission. Various protocols, which are used for 2G or 3G wireless communication, refer to CDMA.
10) What do you understand by demodulating a signal?
Demodulation of a signal is a method of extracting the original information of signal from a carrier wave. An electronic circuit which is used for demodulation is called as a demodulator.
11) What do you understand by telecommunications?
Telecommunication refers to the transmission of any signal, data or any type of information by physical or wireless medium over a significant distance. When the exchange of information between the sender and the receiver occurs with the help of technology, then it is known as telecommunication. In telecommunication there is a communication arrangement with a transmitter and a receiver. At any station, a device which combined the transmitter and receiver is termed as a transceiver.
Basic Elements of Telecommunication System:
- Transmitter: Which takes the information and convert into the form of a signal
- Transmission medium: A medium over which signal travels it may be an optical fibre cable, or free space.
- Receiver: Which receives the signal and convert into a usable form.
12) What are the various advantages of GSM?
GSM is an acronym of Global System for Mobile communication. It defines the standard protocols for the second-generation digital cellular network used by mobile devices.
Advantages of GSM:
- GSM allows a reliable and efficient way to transfer data. It also allows transferring text and pictures.
- GSM provides better security during the conversation. It ensures that only the caller and receiver are in conversation during a call.
- GSM provides the worldwide facility of calls and data transfer, but it may cost high on the international level.
- GSM cell phone has clear sound quality, as it filters background noise.
13) What are the various applications of DSP?
DSP is termed as Digital Signal Processing. It is a part of signal processing which is used to perform a variety of signal processing. DSP unit analyses and modifies a signal to increase its performance and efficiency.
Various applications of DSP in communication:
- DSP is used in audio signal processing.
- DSP is used in encoding the waveforms.
- DSP is used for Audio compression.
- DSP is used for Digital image processing.
- DSP is used for speech processing.
- DSP is used in RADAR, biomedicine, weather forecasting, and many more applications.
14) What do you understand by commands?
Commands are the specific instructions given by the user to the computer?s operating system, to perform a particular task. We can input these commands using the command line interface provided by the operating system.
15) Why we use Jump statement in C++?
Jump statements are used to disturb the normal flow of program unconditionally. There are three types of Jump statements available in C++.
- Break
- Continue
- goto.
16) What do you understand by MAC address?
MAC address stands for “Media Access Control” Address is a unique identification hardware number, which uniquely identifies each device on a network. The MAC address is a computer’s unique hardware number which can be determined by Ethernet or Wi-Fi card. A MAC address is of 64 or 48 bits, which is expressed in hexadecimal forms separated by colons such as 2AA:EF:EF3E:2A1B.
17) What do you understand by nested loop?
If a loop exists inside another loop, then it is termed as a nested loop. Or a loop within a loop is called a nested loop. When we use a nested loop in our code then control passes to the outer loop, then for first iteration it executes its following loop and other conditions and so on and repeats until the outer loop finishes.
Syntax:
- for(int i=0; i<=10; i++)
- {
- For (int j=1; j<I; j++)
- {
- // statement to be executed
- }
- }
18) Why C language is called a procedural language?
A procedural language means a language which follows a procedure of steps and C is called as Procedural language as it follows a specific pattern of top-down for writing code in it. C language gives more priority to the flow of code rather than data. If we do not follow the pattern then it generates the error.
19) What do you understand by JVM?
JVM is termed as Java Virtual Machine, it is a virtual machine which provides a runtime environment to execute a Java application. JVM is a part of JRE (java runtime environment), which compile the code into Java bytecode for computer’s processor.
JVM mainly perform two functions:
- It allows the java program to execute on any platform
- It manages and optimizes the program memory.
JVM is responsible for performing the following three activities:
- Loading the code
- Verification and Execution of code
- Provide the runtime environment for application
20) What is the size of the void pointer in C language?
The size of the void pointer depends upon on which platform you are executing the code. The void pointer may have a size of 2 bytes for the 16-bit compiler, 4 bytes for the 32-bit compiler, and 8 bytes for the 64-bit compiler. To check the size of the void pointer, we can use the sizeof operator.
21) Which type of motor can be used for a lift?
In previous time DC motors were used for lift, but it might cause a jerk, so the latest elevators or lift are designed with a 3-phase induction motor with variable frequency.
22) What do you understand by modulation?
Modulation is a process of changing some characteristics such as amplitude, phase, or frequency of a carrier signal with respect to message signal. The main information consists by the message signal and career signal is just used to transmit that low energy message signal to a particular distance without any distortion. In the modulation process, only the carrier signal characteristics can be changed, but the original message characteristic will remain the same.
Types of modulation:
- Amplitude modulation
- Frequency modulation
- Phase modulation
- Pulse-code modulation
23) What are the various OSI layers and protocols?
The OSI model stands for Open System Interconnection Model. It is a conceptual framework of seven layers which defines the network communication between two systems. The seven different layers perform different tasks using various protocols.
The Layers with their protocols are given below:
- Physical layer: This is the lowest layer of the OSI model which is responsible for transmission and reception of raw data between a device and physical media. This layer converts the raw data into 0 and 1?s bit form. The primary technologies used in the physical layer are Ethernet, Cables, and Hubs, etc.
- Data Link layer: This layer obtains data from the physical layer. It checks and corrects the errors occurs in the physical layer. Data link layer is responsible for node-to-node data transfer. It converts the bits into the form of frames. This layer includes technologies such as PPP, FDDI, IEEE 802.5/802.2, and HDLC, etc.
- Network layer: The network layer is responsible for routing the packets. It moves the packets from source to destination with the source and destination address. The protocols used in this layer are IP (Internet protocol), ICMP, ARP (Address Resolution Protocol), etc.
- Transport layer: This layer takes services from Network layer and provides services to the upper layer. This layer offers host-to-host communication services to the upper layers. It provides connection-oriented communication, reliability and flow control of data packets. The main protocols of the transport layer are TCP (Transmission Control Protocol), UDP (User Datagram control Protocol), DCCP (Datagram Congestion Control Protocol), and SCTP (Stream Control Transmission Protocol).
- Session layer: This layer maintains proper communication by establishing, managing and terminating sessions between computers. The communication session consists of request and response which occurs between different applications. This layer is responsible for Session Check pointing and recovery. The protocols for session layers are AppleTalk, and Session Control Protocol (SCP).
- Presentation layer: This layer is responsible for the delivery and formatting the data to the Application layer as per requirement. This layer transforms the data into the form which application layer accepts. It may use syntax and semantics. Encryption and decryption of data occur at this layer.
- Application layer: This is the topmost layer of the OSI model and closest to end user. This layer directly interacts with the software application. This layer allows the end user to use the network resources. The main protocols used at this layer are HTTP (Hypertext Transfer Protocol), FTP (File Transfer Protocol), SMTP (Simple Mail Transfer Protocol), Telnet.
24) How many numbers of output pins microprocessor 8085 contains?
There are 27 output pins in the 8085 microprocessor.
25) Explain Deadlock?
Deadlock is a state where two processes share the same resources and wait for other to complete before proceeding, and hence the complete process hangs. Such condition is termed as deadlock condition. The deadlock condition occurs mainly in concurrency or multitasking programming.
26) What do you understand by threads?
A thread is a lightweight process or, smallest processing unit. A process can have multiple threads in an operating system. The threads are independent of each other and can share their resources such as memory.
27) What are the various types of Antennas?
An antenna is like a transducer which receives the radio waves propagating through space and convert into electric alternating current or vice-versa. The antenna can be of receiver antenna or transmitter antenna.
Following are the various types of antennas:
- Log-Periodic Antennas
- Wire Antennas
- Traveling wave antennas
- Microwave antenna
- Reflector Antenna
- Other antennas
28) What is the need for 5G technology?
The next generation in mobile network technology will be 5G. The 5G technology will take a boom in every area, after the 4G technology. Although the 4G technology is still developing in many countries and also provides a very high speed, but 5G technology will not only gives a very high speed of 1-10Gbps (approx. in the field) but also make easier and real-time experiences of IoT, Virtual reality with minimum energy usage, and many other advanced features.
29) Why we use multiplexers?
A multiplexer is a combinational logic circuit which selects one of the various analog or digital input signals and produces a single output.
The need of Multiplexers:
- The multiplexer is used to reduce the number of electrical connections/ wireless channels for transmission of various signals.
- It reduces the cost of the system and also increases efficiency.
30) Differentiate between 2G, 3G, and 4G?
The 2G, 3G, and 4G are different generations of mobile networks which shows different strength and speed of data transfer, where G stands for generation. The following are some main differences between 2G, 3G, and 4G mobile technologies.
| 2G Technology | 3G Technology | 4G Technology |
|---|---|---|
| It refers to second-generation mobile technology. | It refers to third-generation mobile technology. | It refers to fourth-generation mobile technology. |
| Data transmission speed of 2G technology was upto 64kbps. | Data transmission speed was upto 144kbps – 3Mbps. | Data transmission speed is 100 Mbps- 1 Gbps. |
31) What do you understand of Spread-spectrum?
In Communication, spread-spectrum is a technique by which a signal generated with a particular bandwidth, is deliberately varied in frequency domain resulting in a signal with the wider bandwidth. The spread spectrum techniques are useful for the establishment of secure communication, limit the power flux density, and prevent detection.
32) How packets travel through the network?
The information travels through the internet in the form of the packets and travels through the different OSI layers. When we send a message or any information it breaks into the form of packets. These packets are wrapped which contains header and footer, which tells the
- information type,
- its source address and
- destination address
The packets from the same message follow the different routes, and these packets will travel through the internet until they will not reached to their destination. At destination the packets are recreated and unwrapped to find the original information. While travelling the packets through the internet if one path is blocked then the packets follow alternate route. The machine which is receiving the data will identify if any packet is missing and will send a signal to resend the data. This is the complete process by which data travels through the network.
33) Write a program to print Fibonacci series upto n elements?
- #include<stdio.h>
- int main()
- {
- int n1=0,n2=1,next_term,i,number=10;
- printf(“\n Series is %d %d”,n1,n2); //print 0 and 1
- for(i=2;i<number;++i)
- {
- next_term=n1+n2;
- printf(” %d”,next_term);
- n1=n2;
- n2=next_term;
- }
- return 0;
- }
Output:
Series is 0 1 1 2 3 5 8 13 21 34
34) Write a program which generates divisor of an integer?
- #include <stdio.h>
- int main() {
- int i, n=50;
- for(i=1; i<=n;i++){
- if(n%i==0){
- printf(” %d”, i);
- }
- }
- return 0;
- }
Output:
1 2 5 10 25 50
35) Why do we use the Bode plot? Explain its Significance?
In electrical engineering, a Bode plot is a graph which shows the frequency response of the LTI system. It consists of two plots:
- Bode magnitude plot which express magnitude of the frequency response.
- Bode Phase plot which shows the phase shift.
The significance of bode plot is that it shows the gain and phase response of a LTI system for various frequencies.
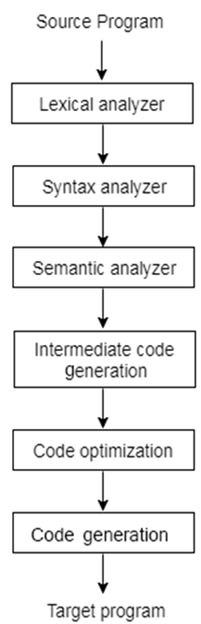
36) What are the different phases of the compiler?
A compiler operates in various phases. The phases are interrelated operation that takes source program as input and generates the output passing through various phases. There are mainly two compilation phases:
- Analysis Phase
- Synthesis Phase
The complete compiler has several phases which are given below:
- Lexical Analysis
- Syntax Analysis
- Semantic Analysis
- Intermediate Code Generation
- Code Optimization
- Code Generation
37) Explain the cellular network?
A cellular network is a communication network for mobile phones and wireless network where the last link is wireless. Cellular network provides communication services using large number of base stations, and use limited power where each base station covers a small area. Each small area in cellular network is called as a cell. In cellular network, it re-use the same frequency for another cell which is away from that base station without any interference. By this phenomenon a large geographical area can be covered with a very limited range of frequency. The following are the key points for cellular network:
- Cellular network use multiple low power transmitters.
- The complete area is divided into small cells.
- The adjacent cells are provided with different frequency to stop the interferences.
- The cells which are far away from each other are provided the same frequency which re-use the frequency.